Vault kasutamine
Sissejuhatus
TODO
Vault teenus
Testiks vault käivitamiseks sobib öelda dockerhostis
# docker run -p 8200:8200 -e 'VAULT_DEV_ROOT_TOKEN_ID=dev-only-token' vault
Tulemusena TODO
vault klient
TODO
Python
Oluline on kasutada sobivat versiooni Pythonit, nt Ubuntu 22.04 paistab toimivat, paigaldatakse hashicorp-vault-client-api teek
# apt-get install python3-hvac
Test skript
# cat example.py
import hvac
import sys
# Authentication
client = hvac.Client(url='http://192.168.110.221:8200', token="dev-only-token")
print(client.is_authenticated())
# Writing a secret
create_response = client.secrets.kv.v2.create_or_update_secret(
path='my-secret-password-imre',
secret=dict(password='Hashi123'),
)
print('Secret written successfully.')
# Reading a secret
read_response = client.secrets.kv.v2.read_secret_version(path='my-secret-password-imre',)
password = read_response['data']['data']['password']
if password != 'Hashi123':
sys.exit('unexpected password')
print('Access granted!')
Kasutamine
# python3 example.py True Secret written successfully. Access granted!
Ansible kasutamine
# cat hw.yml
---
- name: Hello World!
hosts: all
tasks:
- name: Hello World!
shell: echo "Hi! Tower is working."
- name: imre test
debug:
msg: "{{ lookup('hashi_vault', 'secret=secret/data/my-secret-password-imre token=dev-only-token url=http://192.168.110.221:8200')}}"
# cat hosts
[dockerhost]
192.168.110.221
# ansible-playbook hw.yml
PLAY [Hello World!]
****************************************************************************
TASK [Gathering Facts]
****************************************************************************
TASK [Hello World!]
****************************************************************************
changed: [192.168.110.221]
TASK [imre test]
****************************************************************************
ok: [192.168.110.221] => {
"msg": {
"password": "parool"
}
}
PLAY RECAP
****************************************************************************
192.168.110.221 : ok=3 changed=1 unreachable=0 failed=0 skipped=0 rescued=0 ignored=0
2026 aasta kevadel tähelepanekud
Tööpõhimõte
- dev - andmed on volatiilsed st ei ela rebooti üle
- non-dev - andmed on püsivalt salvestatud (järgnev tegeleb selle juhtimiga)
Vault tarkvara sisaldab nn raft andmesalvestuse võimekust.
non-dev kasutamine docker compose abil
root@dh-jenkins-01:/srv/vault/dc# cat docker-compose.yml
name: p_vault
services:
svc_vault:
image: hashicorp/vault:latest
container_name: cn_vault
ports:
- "8200:8200"
volumes:
- /srv/vault/volume/vault/config:/vault/config
- /srv/vault/volume/vault/data:/vault/data
- /srv/vault/volume/vault/logs:/vault/logs
environment:
- VAULT_ADDR=http://127.0.0.1:8200
- VAULT_API_ADDR=http://127.0.0.1:8200
cap_add:
- IPC_LOCK # CRITICAL: Prevents Vault from swapping secrets to disk
command: server
networks:
- nw_vault
networks:
nw_vault:
name: nw_vault
driver: bridge
ning lisaks on vault tarkvara seadistusfail
root@dh-jenkins-01:/srv/vault/dc# cat /srv/vault/volume/vault/config/vault.hcl
disable_mlock = false
storage "raft" {
path = "/vault/data"
node_id = "node1"
}
listener "tcp" {
address = "0.0.0.0:8200"
tls_disable = "true" # Set to "false" and add certs once you're out of dev/test mode
}
api_addr = "http://127.0.0.1:8200"
cluster_addr = "https://127.0.0.1:8201"
ui = true
Käivitada
# docker-compose up -d
kus
- esitatakse root kasutaja token (millega saab webgui peale sisse logida)
- esitatakse 5 saladus, neid kasutatakse andmebaasi aktiveerimiseks
initsialiseerimine
# docker exec -it hashicorp-vault vault operator init
andmebaasi seal eemaldamine
# docker exec -it hashicorp-vault vault operator unseal
policy tekitamiseks tuleb liikuda webgui keskkonnas
Policies -> ACL Policies -> Create ACL Policy +
ning sisestada nimeks nt 'admin-policy' ja sisuks
# Manage secrets engines
path "sys/mounts/*" {
capabilities = ["create", "read", "update", "delete", "list", "sudo"]
}
# List, create, update, and delete key/value secrets
path "secret/*" {
capabilities = ["create", "read", "update", "delete", "list", "sudo"]
}
# Manage auth methods
path "sys/auth/*" {
capabilities = ["create", "read", "update", "delete", "list", "sudo"]
}
# Create and manage policies
path "sys/policies/acl/*" {
capabilities = ["create", "read", "update", "delete", "list", "sudo"]
}
Kasutaja tekitamiseks tuleb esmalt aktiveerida kasutajanimi+parool põhine autentimise meetod
Access -> Authentication Methods -> Enable new method -> Userpass -> Use as preferred UI login method
Kasutaja lisamiseks
Access -> Authentication Methods -> userpass/ -> > Create user -> Generated Token's Policies -> admin-policy
Saladusi hoitakse nn engine'ite sees, näiteks, sellise engine moodustamiseks sobib valida
Secrets Engines -> Enable new engine -> KV -> test
kusjuures selleks, et kasutaja saaks seda kasutada peab olema see kasutaja policy juures lubatud, nt lisada sinna lõik
path "test/*" {
capabilities = ["create", "read", "update", "delete", "list", "sudo"]
}
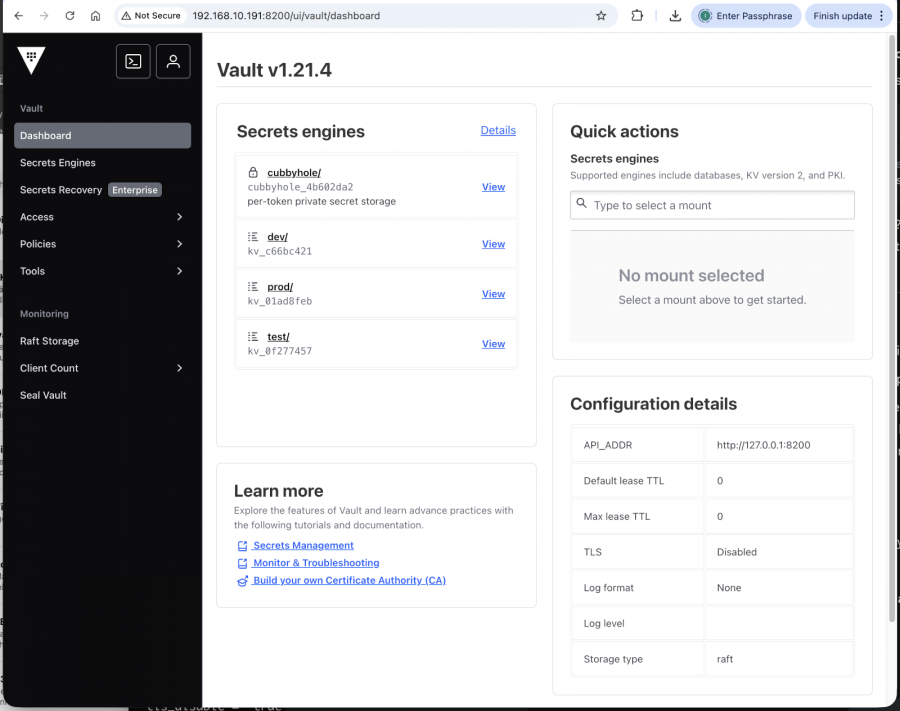
Peale mõningast sättimist paistab root kasutajale vault dashboard selline
kus
- TODO